TACACS Client Configuration
Overview
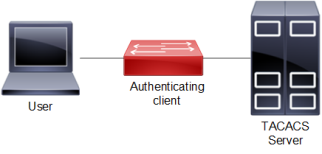
Terminal Access Controller Access Control System (TACACS![]() Terminal Access Controller Access Control System) is a remote authentication protocol that is used to communicate with an authentication server. With TACACS, a network device communicates to an authentication server to determine whether a particular user should be allowed access to the device. TACACS+ listens at port 49.
Terminal Access Controller Access Control System) is a remote authentication protocol that is used to communicate with an authentication server. With TACACS, a network device communicates to an authentication server to determine whether a particular user should be allowed access to the device. TACACS+ listens at port 49.
TACACS Server Authentication
IPv4 Address Configuration
TACACS server address is configured as IPV4 address.
Topology
Figure 6. TACACS Server Host Configuration
Authenticating Device
|
#configure terminal |
Enter configure mode. |
|
(config)#feature tacacs+ |
Enable the feature TACACS+ for default vrf |
|
(config)#tacacs-server login key 0 testing101 |
Specify the global key for tacacs servers that are not configured with their respective keys for default vrf This key should match the one present in the config file of tacacs server |
|
(config)#tacacs-server login host 10.16.19.2 seq-num 1 key 0 testing123 |
Specify the tacacs server ipv4 address to be configured with shared key. The same key should be present on the server config file |
|
(config)#tacacs-server login host 10.12.30.86 seq-num 4 port 1045 |
Specify the tacacs server ipv4 address to be configured with the sequence and port number.The tacacs server should be started with same port number |
|
(config)#tacacs-server login host 10.12.30.86 seq-num 2 port 1045 |
Specify the tacacs server ipv4 address to be configured with the sequence and port number for default vrf. The tacacs server should be started with same port number |
|
(config)#tacacs-server login host 10.12.17.11 seq-num 8 key 7 65535 port 65535 |
Specify the tacacs server ipv4 address to be configured with the sequence, key and port number for default vrf. The tacacs server should be started with same port number. |
|
(config)#tacacs-server login host Tacacs-Server-1 seq-num 7 key 7 65535 port 65535 |
Specify the tacacs server configured with host-name sequence number key and port number for default vrf. The tacacs server should be started with same port number |
|
(config)#aaa authentication login default group tacacs+ |
Enable authentication for TACACS+ server configured for default vrf. Authorization is also enabled by default |
|
(config)#aaa authentication login default group tacacs+ local |
Enable authentication for TACACS+ and fall-back to local configured for default vrf. Authorization is also enabled by default |
|
(config)#aaa authentication login default group tacacs+ local none |
Enable authentication for TACACS+ fall-back to local followed by fall-back to none configured for default vrf. Authorization is also enabled by default |
|
(config)#aaa authentication login default group tacacs+ none |
Enable authentication for TACACS+ fall-back to none configured for default vrf. Authorization is also enabled by default |
|
(config)#aaa group server tacacs+ G1 |
Create aaa group G1 for default vrf |
|
(config-tacacs)#server 10.12.30.86 |
Make the tacacs-server 10.12.30.86 a part of this group G1 for default vrf |
|
(config-tacacs)#server Tacacs-Server-1 |
Make the tacacs-server Tacacs-Server-1 a part of this group G1 for default vrf |
|
(config-tacas)#exit |
Exit the tacacs-config |
|
(config)#commit |
Commit the candidate configuration to the running configuration. |
|
(config)#aaa authentication login default group G1 |
Authenticate the tacacs+ group G1 with aaa authentication for default vrf |
|
(config)#commit |
Commit the candidate configuration to the running configuration. |
Users are mapped as shown as shown in Table 11. Role/privilege level mapping:
|
Role |
Privilege level |
|
Network administrator |
15 |
|
Network engineer |
14 |
|
Network operator |
1 to 13 |
|
Network user |
0 or any other values (>15 or negative values or any character) |
Validation
Leaf1#show tacacs-server
VRF![]() Virtual Routing and Forwarding: default
Virtual Routing and Forwarding: default
total number of servers:2
Tacacs+ Server : Tacacs-Server-1/2222
Sequence Number : 7
Failed Auth Attempts : 0
Success Auth Attempts : 0
Failed Connect Attempts : 0
Last Successful authentication:
Tacacs+ Server : 100.0.0.1/2222
Sequence Number : 8
Failed Auth Attempts : 0
Success Auth Attempts : 0
Failed Connect Attempts : 0
Last Successful authentication:
(*) indicates last active.
#show tacacs-server vrf all groups G1
VRF: default
group G1:
server Tacacs-Server-1:
seq-num 7
port is 2222
key is ********
server 100.0.0.1:
seq-num 8
port is 2222
key is ********
#show tacacs-server groups G1
VRF: default
group G1:
server Tacacs-Server-1:
seq-num 7
port is 2222
key is ********
server 100.0.0.1:
seq-num 8
port is 2222
key is ********
#show tacacs vrf all
VRF: default
total number of servers:2
Tacacs+ Server : Tacacs-Server-1/2222(*)
Sequence Number : 7
Failed Auth Attempts : 0
Success Auth Attempts : 1
Failed Connect Attempts : 0
Last Successful authentication: 2018 October 30, 10:32:52
Tacacs+ Server : 100.0.0.1/2222
Sequence Number : 8
Failed Auth Attempts : 0
Success Auth Attempts : 0
Failed Connect Attempts : 0
Last Successful authentication:
(*) indicates last active.
#show tacacs
VRF: default
total number of servers:2
Tacacs+ Server : Tacacs-Server-1/2222(*)
Sequence Number : 7
Failed Auth Attempts : 0
Success Auth Attempts : 1
Failed Connect Attempts : 0
Last Successful authentication: 2018 October 30, 10:32:52
Tacacs+ Server : 100.0.0.1/2222
Sequence Number : 8
Failed Auth Attempts : 0
Success Auth Attempts : 0
Failed Connect Attempts : 0
Last Successful authentication:
(*) indicates last active.
#show aaa authentication vrf all
VRF: default
default: group tacacs+
#show aaa authentication
VRF: default
default: group tacacs+
console: local
# show aaa groups vrf all
VRF: default
radius
tacacs+
G1
#show aaa groups
VRF: default
radius
tacacs+
G1
#show running-config aaa all
aaa authentication login default group tacacs+
aaa authentication login console local
aaa accounting default local
no aaa authentication login default fallback error local
no aaa authentication login console fallback error local
no aaa authentication login error-enable
aaa local authentication attempts max-fail 3
aaa local authentication unlock-timeout 1200
aaa group server tacacs+ G1
server Tacacs-Server-1
server 100.0.0.1
IPv6 Address Configuration
TACACS+ server address is configured as IPV6 address. Authentication messages are transmitted to TACACS+ server from the Router using IPv6 address.
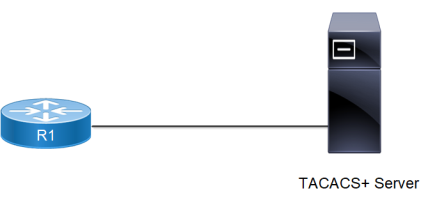
Topology
Figure 7. TACACS+ server topology
Figure 7. TACACS+ server topology shows the sample configuration of TACACS+ server.
DUT
|
R1#configure terminal |
Enter configure mode. |
|
R1(config)#feature tacacs+ |
Config for enabling the TACACS+ server |
|
R1(config)#tacacs-server login host 2001:db8:100::2 seq-num 1 key 0 testing123 |
Configure TACACS+ server with IPv6 address |
|
R1(config)# aaa authentication login default group tacacs+ |
Configure AAA authentication |
|
R1(config)#tacacs-server login host 2001:db8:100::2 seq-num 1 |
Config for IPv6 TACACS server with seq-num |
|
R1(config)# ip host Server1 2001:db8:100::2 |
Config for assigning hostname to valid IPv6 address |
|
R1(config)#feature tacacs+ |
Config for enabling the TACACS+ server |
|
R1(config)#tacacs-server login host 2002::3 seq-num 5 key 0 def_abc port 65535 timeout 60 |
Config for IPv6 TACACS+ server address with key, port and timeout |
|
R1(config)#tacacs-server login timeout 60 |
Config timeout for TACACS server |
|
R1(config)#tacacs-server login key 7 65535 |
Config login key for TACACS server |
|
R1(config)# interface eth0 |
Navigate to the interface mode |
|
R1(config-if)#ipv6 address 2001:db8:100::5/64 |
Configure IPv6 address on the eth0 interface |
|
R1(config-if)#exit |
Exit interface configure mode |
|
R1(config)#commit |
Commit the candidate configuration to the running configuration. |
|
R1(config)# exit |
Exit configure mode |
Validation
Perform TELNET to the Router. Provide the username mentioned in the TACACS+ server "users" file as telnet username. Check that Router sends TACACS request to the TACACS server using IPv6 address.
#show running-config tacacas+
tacacs-server login host 2002::3 seq-num 1 key 7 0x6f32ba3f9e05a3db
#sh tacacs-server
VRF: default
total number of servers:1
Tacacs+ Server : 2002::3/49
Sequence Number : 1
Failed Auth Attempts : 0
Success Auth Attempts : 0
Failed Connect Attempts : 0
Last Successful authentication:
(*) indicates last active.
#show running-config aaa
aaa authentication login default group tacacs+
aaa authentication login error-enable
#show ipv6 interface eth0 brief
Interface IPv6-Address Admin-Sta
tus
eth0 2001:db8:100::5
fe80::218:23ff:fe30:e6ba [up/up]
TACACS Server Accounting
After authentication, the user can configure accounting to measure the resources that the user consumes during access.
Authenticating Device
|
#configure terminal |
Enter configure mode. |
|
(config)#feature tacacs+ |
Enable the feature TACACS+ for default vrf |
|
(config)#tacacs-server login host 10.16.19.2 seq-num 1 key 0 testing123 |
Specify the TACACS server IPv4 address to be configured with shared key for default vrf. The same key should be present in the server configuration file. |
|
(config)#tacacs-server login host 10.16.19.2 seq-num 3 key 0 testing123 |
Specify the TACACS server IPv4 address to be configured with shared key default vrf. The same key should be present in the server configuration file. |
|
(config)#aaa accounting default group tacacs+ |
Enable accounting for TACACS server configured for default vrf. |
|
(config)#commit |
Commit the candidate configuration to the running configuration. |
|
(config)#exit |
Exit configure mode |
|
#clear tacacs-server counters |
Clear tacacs server counters for default vrf. |
|
#clear tacacs-server counters vrf all |
Clear tacacs server counters for default vrf. |
To verify the TACACS accounting process, connect using SSH or Telnet from the host to the client with the user created and provided TACACS server password, and check whether the client validates the user with corresponding username and password.
Validation Commands
show tacacs-server, show aaa accounting, show aaa accounting
#show aaa accounting vrf all
VRF: default
default: group tacacs+
#show aaa accounting
VRF: default
default: group tacacs+
#
#show running-config aaa
aaa authentication login default group tacacs+
aaa accounting default group tacacs+
aaa group server tacacs+ G1
server Tacacs-Server-1
server 100.0.0.1
Sample TACACS Config File Contents
#tacacs configuration file
#set the key
key = "testing123"
accounting file = /var/log/tac_acc.log
user = test1 {
default service = permit
login = cleartext "12345"
}
group = netadmin {
service = ppp protocol = ip {
priv-lvl = 1
}
}
user = test2 {
default service = permit
login = cleartext "12345"
member = netadmin
}
user = test3 {
default service = permit
login = cleartext "12345"
service = ppp protocol = ip {
priv-lvl = 15
}
}
TACACS Server Authorization
Authorization is realized by mapping the authenticated users to one of the existing predefined roles as shown in Table 11. Role/privilege level mapping.
The privilege information from the TACACS+ server is retrieved for the authenticated users and is mapped onto one of the roles as shown in Table 11. Role/privilege level mapping.
Each authenticated user is mapped to one of the pre-defined privilege level.
Users with priv-level <=0 and priv-level > 15 are treated as read-only user mapped onto the pre-defined network-user role.
There is no command to enable authorization. Authorization functionality is enabled by default when remote authentication is enabled with TACACS+.
Authorization is “auto-enabled”. After successful authentication, a user can enter into privilege exec mode, irrespective of its privilege level and such user is not prompted with enable mode password, if configured. However based on their role, commands are rejected if not allowed to perform certain operations.
Example
A network-user has read-only access and can only execute show commands. A network-user cannot enter configure mode. An error message is displayed upon executing any command which is not allowed.
#write
% Access restricted for user %
#configure terminal
% Access restricted for user %
The following attribute value pair in TACACS+ server is used to fetch user privilege information.
service = ppp protocol = ip {
priv-lvl = <0…15>
}
Sample TACACS+ Configuration File
#tacacs configuration file from “tac_plus version F4.0.3.alpha “
#set the key
key = "testing123"
accounting file = /var/log/tac_acc.log
#Read only user “test1”, without any priv-lvl, mapped to role “network-user”
user = test1 {
default service = permit
login = cleartext "12345"
}
#We can create a group of users mapped to a privilege
group = netadmin {
service = ppp protocol = ip {
priv-lvl = 15
}
}
#User “test2” with highest priv-lvl=15, mapped to role “network-admin”
user = test2 {
default service = permit
login = cleartext "12345"
member = netadmin
}
#User “test3” with priv-lvl= 1…13, mapped to role “network-operator”
user = test3 {
default service = permit
login = cleartext "12345"
service = ppp protocol = ip {
priv-lvl = 10
}
}
#User “test4” with priv-lvl=14, mapped to role “network-engineer” user = test4 {
default service = permit
login = cleartext "12345"
service = ppp protocol = ip {
priv-lvl = 14
}
}